Why StackOverflow is Toxic, and a Way to Improve It
People ask questions when they don’t know enough to solve a problem on their own. This means, by definition, they are very likely not to…
- March 2, 2024 4:44 pm·
- 0 comments·
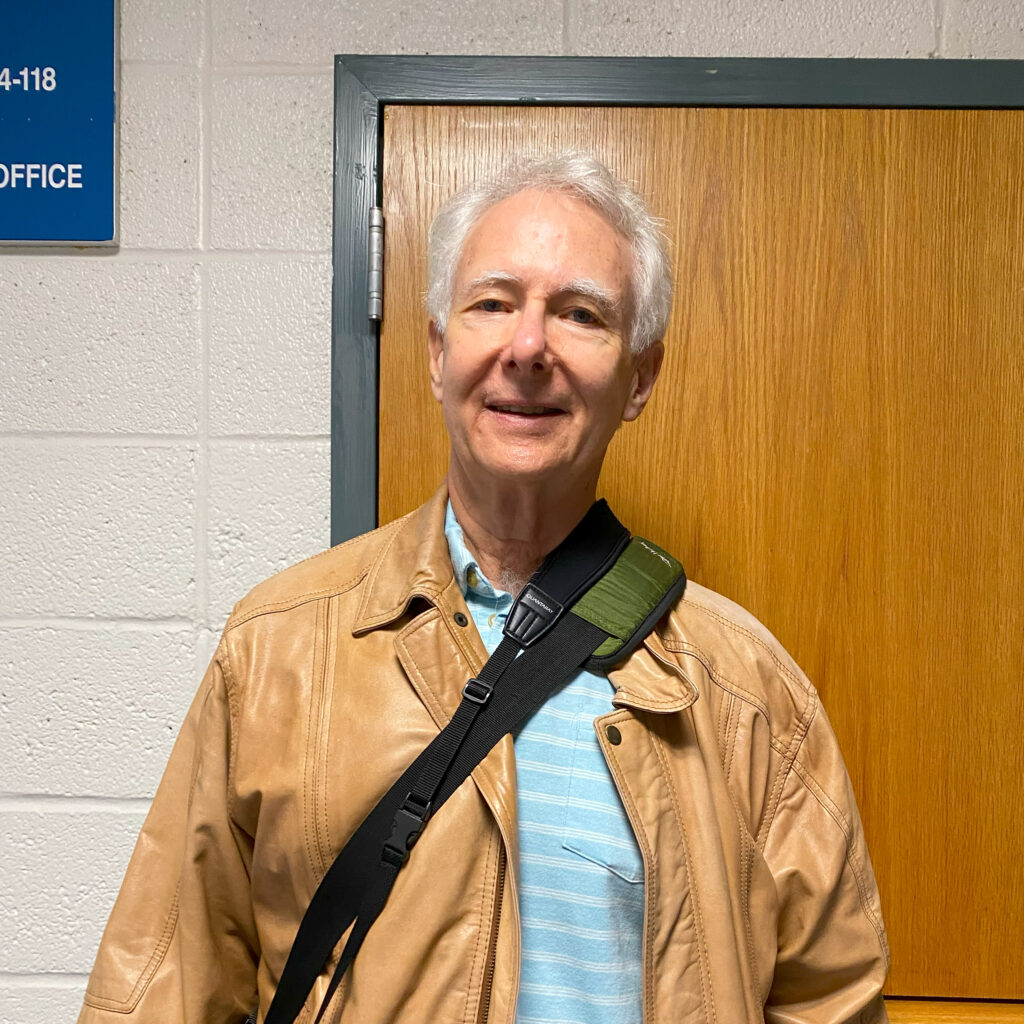
Where It All Began
I recently attended my 50th high school reunion, which, among other things, included a tour of the school itself. I actually started going to the…
- October 11, 2023 8:27 pm·
- 2 comments·

A Thousand Suns Isn’t Even Close
You know that phrase “I [hate|despise] you with the fire of a thousand suns”? Well, that doesn’t begin to describe the way I feel about…
- August 8, 2023 2:54 am·
- 0 comments·

OMG, It Works!
Which is not at all what I expected when I hit F5 to debug an app just now. One mark of a well-architected software package,…
- June 2, 2023 3:52 pm·
- 0 comments·
Keychron Keyboard: Yet Another Exercise in Frustration
I’ve had my eye on a clickier keyboard for some time. But I put it off because it was hard to find a place where…
- March 25, 2023 6:30 pm·
- 0 comments·
A Better WordPress Debug/Diagnostic Environment
I’ve used WordPress for years. I’m also a long-term amateur programmer, mostly specializing in C# these days. One of the wonderful things about WordPress is…
- October 17, 2022 4:17 pm·
- 0 comments·