Dealing with Stalled Debian Upgrades
I periodically encounter, when upgrading my Debian systems, situations where the upgrade process stalls. As I recall, this generally happens when upgrading initramfs, but I
I periodically encounter, when upgrading my Debian systems, situations where the upgrade process stalls. As I recall, this generally happens when upgrading initramfs, but I

I’ve been a Visual Studio Professional licensee for decades. For almost all those years my license simply autorenewed (although I did have a bit of

I use postfix and dovecot to provide email capabilities on various blogs I manage. Recently, I noticed a large number of failed postfix login attempts.
This story involves Debian 12, running on a VPS at Hostwinds.com. I was getting ready to spin up a new WordPress site and was doing
It’s been a while since I played bongos on the (virtual) heads of Microsoft’s documentation staff, but that wasn’t for lack of their continued striving

I recently started trying to use the MSBuild API in a project where I need to be able to parse csproj files and then do
People ask questions when they don’t know enough to solve a problem on their own. This means, by definition, they are very likely not to
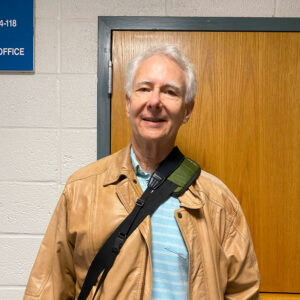
I recently attended my 50th high school reunion, which, among other things, included a tour of the school itself. I actually started going to the

You know that phrase “I [hate|despise] you with the fire of a thousand suns”? Well, that doesn’t begin to describe the way I feel about

Which is not at all what I expected when I hit F5 to debug an app just now. One mark of a well-architected software package,